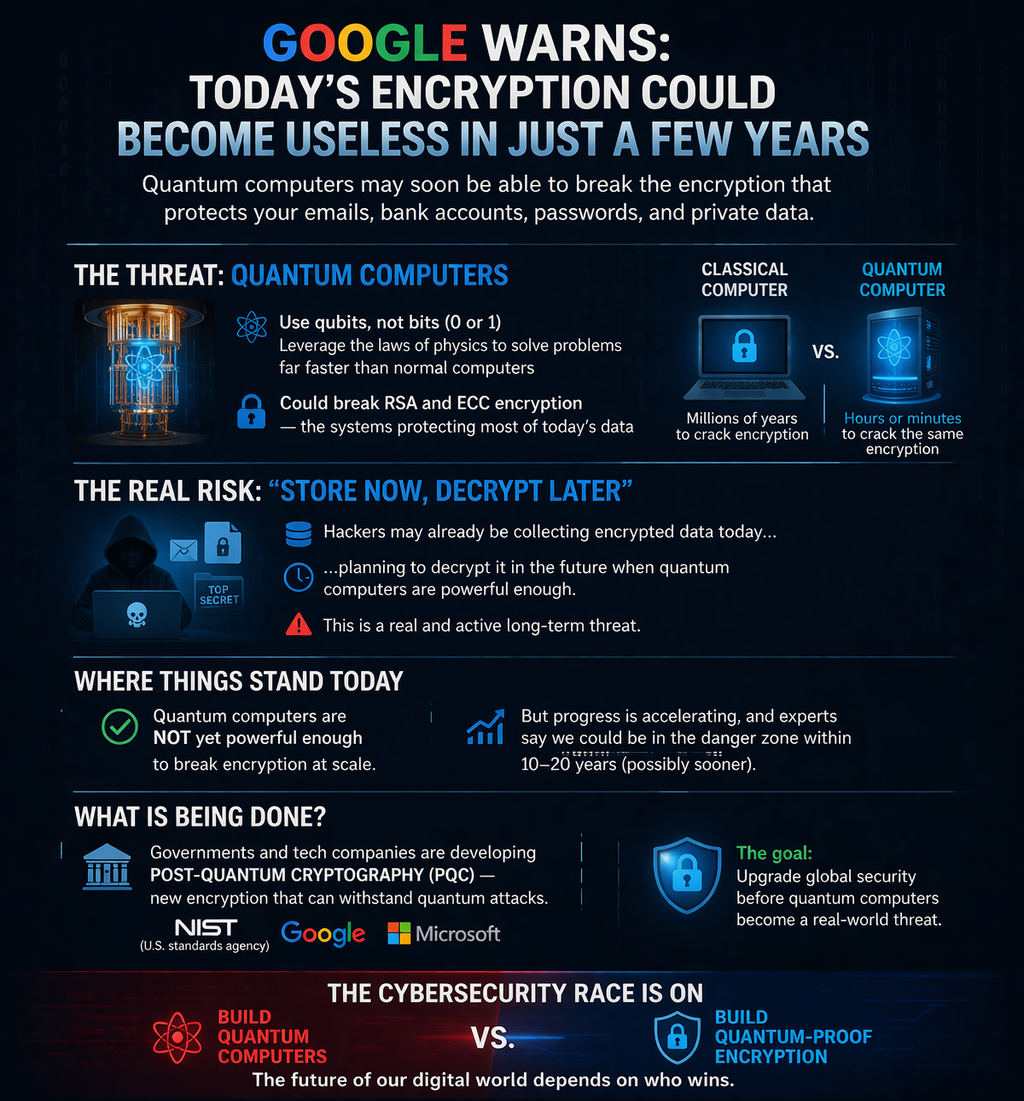
- Normal computers → use bits (0 or 1)
- Quantum computers → use qubits (0 AND 1 at the same time)
This allows them to solve certain problems exponentially faster.
🔐 Why encryption is at risk
Today’s internet security (banking, passwords, emails) relies on systems like:
These are secure because classical computers would take millions of years to break them.
But a powerful quantum computer running:
…could break them in hours or minutes.
👉 That’s the core concern.
⚠️ “Store now, decrypt later” — is this real?
Yes, this is a legitimate strategy already discussed in cybersecurity.
- Hackers or governments can collect encrypted data today
- Store it for years
- Decrypt it later when quantum tech matures
This matters especially for:
- Government secrets
- Financial records
- Personal data with long-term value
⏳ But how close are we really?
Here’s the key reality check:
👉 We are NOT there yet
Current quantum computers:
- Have limited qubits
- Are error-prone
- Cannot yet break real-world encryption at scale
Experts estimate:
- 10–20+ years (possibly sooner, possibly later) for a true threat
So:
✔ Risk is real
❌ Immediate collapse of encryption is NOT happening tomorrow
🛡️ What is being done to stop this?
Governments and companies are already preparing.
One major effort:
They are developing post-quantum cryptography (PQC):
- New encryption methods resistant to quantum attacks
Tech giants like:
…are already testing these systems.
🌍 What this means for you (simple version)
- Your data is safe today
- But long-term sensitive data could be at risk
- The world is already transitioning to quantum-safe security
🧠 Final perspective
Think of this like a cybersecurity race:
- One side → building quantum computers
- Other side → building quantum-proof encryption
👉 Whoever wins determines the future of digital security.